Azure App Service: Auto-Scaling, CI/CD, and Integration with GitHub & Azure DevOps
A deep, practical guide to building, deploying, securing, and troubleshooting web apps, APIs, and mobile backends on Azure App Service.
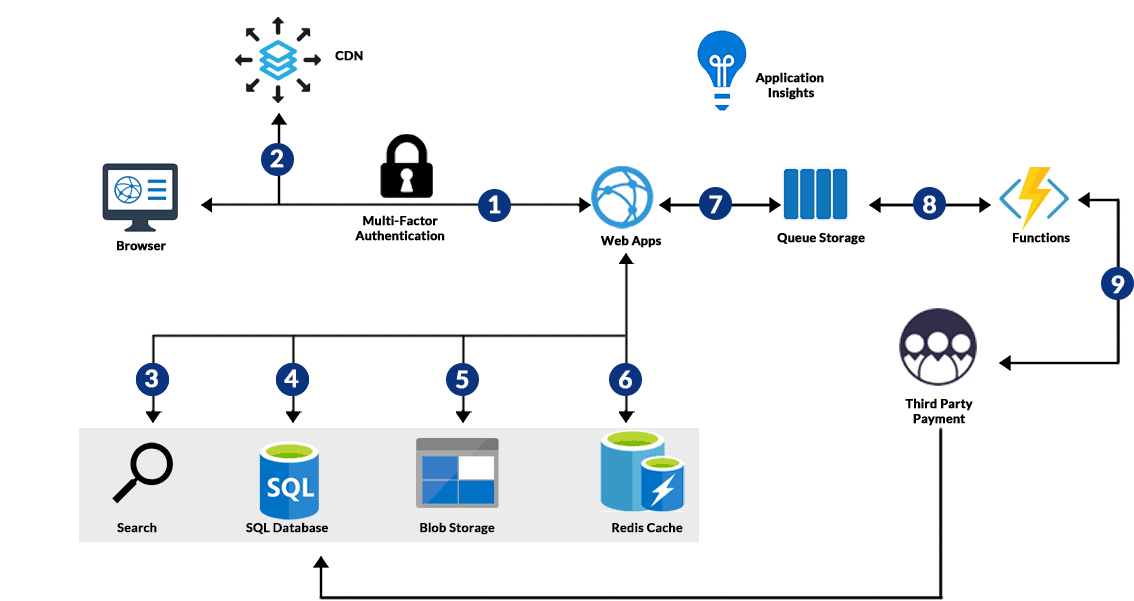
Azure App Service is a fully managed PaaS for hosting modern web apps, REST APIs, and mobile backends with built-in auto-scaling, CI/CD, enterprise-grade security, and rich integration with GitHub Actions and Azure DevOps. This guide gives you a production-ready blueprint: how to choose plans, wire up deployment slots, configure SSL and custom domains, connect to managed databases, monitor with Application Insights, and troubleshoot quickly using PowerShell, Azure CLI, Kudu, Diagnostics, and Graph API.
We’ll also include copy-pasteable snippets for common ops tasks (swap slots, scale rules, health checks, log streaming, managed identity tokens, VNet integration checks, and access reviews). Each topic includes a brief FAQ and “Key Points” so you can skim when you’re under time pressure.
Overview of Azure App Service (Managed PaaS)
Azure App Service abstracts servers, OS patching, scaling infrastructure, and load balancers so developers can focus on shipping code. It supports web apps, API apps, and mobile backends, with deployment via GitHub, Azure DevOps, local Git/ZIP, or containers. You can run Linux or Windows plans, attach managed identities, and connect privately using VNet integration and Private Endpoints.
FAQs
- Q: Is App Service serverless?
A: It’s managed PaaS (always-on). For event-driven serverless, combine with Azure Functions on a Consumption plan, or run Functions on App Service plans for steady workloads. - Q: Linux or Windows plan?
A: Choose Linux for containerized or Node/Python workloads; choose Windows when you need full .NET Framework or certain Windows-only dependencies. - Q: How do I isolate noisy neighbors?
A: Use Premium v3 or Isolated v2 (ASE v3) for dedicated compute and advanced networking.
Key Points
- Managed platform with 99.95% SLA at Standard and above.
- First-class integration with Azure DevOps and GitHub Actions.
- Supports VNet integration, Private Endpoints, and managed identities.
Supports Multiple Frameworks
Host .NET/.NET Core, Java, Node.js, Python, PHP, and Ruby. For custom stacks, use Web App for Containers with Docker images from ACR or Docker Hub. App Service detects runtime versions automatically or via startup scripts.
Troubleshooting Snippet: Verify Runtime
# Azure CLI: Check configured stack/runtime
az webapp config show -g <resourceGroup> -n <appName> --query "{linuxFxVersion: linuxFxVersion, windowsFxVersion: windowsFxVersion, netFrameworkVersion: netFrameworkVersion, javaVersion: javaVersion, nodeVersion: nodeVersion, pythonVersion: pythonVersion}"
FAQs
- Q: Can I pin Node/Python versions?
A: Yes—set in App Service configuration or provide a custom container image. - Q: Does App Service support Ruby?
A: Linux containers are recommended for Ruby apps.
Key Points
- Use Oryx build or your own Dockerfile.
- Startup scripts let you customize boot behavior.
Built-in Auto-Scaling
App Service scales out instances based on CPU, memory, HTTP queue length, or custom metrics from Application Insights. Scale up by moving to higher SKUs (e.g., S1→P1v3). For mission-critical workloads, use multiple regions and a global front door or Traffic Manager.
PowerShell: Create Autoscale Rule
# Requires Az.Resources, Az.Monitor
$rg = "<resourceGroup>"
$asp = "<appServicePlanName>"
$profile = New-AzAutoscaleProfile -Name "default" -DefaultCapacity 2 -MinimumCapacity 2 -MaximumCapacity 10 `
-Rule (New-AzAutoscaleRule -MetricName "CpuPercentage" -MetricResourceId "/subscriptions/<subId>/resourceGroups/$rg/providers/Microsoft.Web/serverfarms/$asp" `
-Operator GreaterThan -Threshold 70 -TimeGrain 00:01:00 -TimeWindow 00:10:00 -Statistic Average -ScaleActionCooldown 00:05:00 -ScaleActionDirection Increase -ScaleActionValue 1),
(New-AzAutoscaleRule -MetricName "CpuPercentage" -MetricResourceId "/subscriptions/<subId>/resourceGroups/$rg/providers/Microsoft.Web/serverfarms/$asp" `
-Operator LessThan -Threshold 35 -TimeGrain 00:01:00 -TimeWindow 00:15:00 -Statistic Average -ScaleActionCooldown 00:10:00 -ScaleActionDirection Decrease -ScaleActionValue 1)
Add-AzAutoscaleSetting -Name "appservice-autoscale" -ResourceGroup $rg -Location "Central India" `
-TargetResourceId "/subscriptions/<subId>/resourceGroups/$rg/providers/Microsoft.Web/serverfarms/$asp" -Profile $profile -Enabled $true
FAQs
- Q: Does scaling cause downtime?
A: No—instances are added/removed behind a load balancer. Keep warm-up in mind for cold starts. - Q: Can I scale by a custom metric?
A: Yes—emit custom metrics to Azure Monitor and reference in rules.
Key Points
- Define both up and down rules to avoid cost spikes.
- Use deployment slots + health checks to protect scaling events.
CI/CD with GitHub Actions & Azure DevOps
Connect your repository to App Service for automated build/test/deploy. With GitHub Actions, use an OIDC-based federated credential so you can deploy with no secret rotation. With Azure DevOps, use service connections to target subscriptions safely.
GitHub Actions (OIDC) – Node.js Example
# .github/workflows/deploy.yml
name: Deploy to Azure App Service
on:
push:
branches: [ "main" ]
permissions:
id-token: write
contents: read
jobs:
build-and-deploy:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- uses: actions/setup-node@v4
with:
node-version: '20'
- name: Build
run: |
npm ci
npm run build
- name: Azure Login (OIDC)
uses: azure/login@v2
with:
client-id: ${{ secrets.AZURE_CLIENT_ID }}
tenant-id: ${{ secrets.AZURE_TENANT_ID }}
subscription-id: ${{ secrets.AZURE_SUBSCRIPTION_ID }}
- name: Deploy to App Service
uses: azure/webapps-deploy@v3
with:
app-name: <appName>
package: .
Azure DevOps Pipelines – .NET Example
# azure-pipelines.yml
trigger:
- main
pool:
vmImage: 'ubuntu-latest'
steps:
- task: UseDotNet@2
inputs:
packageType: 'sdk'
version: '8.0.x'
- script: |
dotnet restore
dotnet build --configuration Release
dotnet publish -c Release -o $(Build.ArtifactStagingDirectory)
displayName: 'Build'
- task: AzureWebApp@1
inputs:
azureSubscription: '<serviceConnection>'
appName: '<appName>'
package: '$(Build.ArtifactStagingDirectory)'
FAQs
- Q: How to avoid secrets in Actions?
A: Use OIDC + federated credentials; avoid PATs and long-lived service principals. - Q: Can I deploy per branch?
A: Map branches to deployment slots (dev/stage/prod) and use approvals for swaps.
Key Points
- Automate tests and smoke checks before slot swap.
- Keep artifacts immutable; version releases clearly.
Zero-Downtime Deployment with Slots
Deployment slots enable safe rollouts: deploy to staging, test, warm up, then swap to production. Slot settings (e.g., connection strings) can be marked “sticky” to prevent cross-contamination.
PowerShell: Create Slot & Swap
# Requires Az.Websites
$rg = "<resourceGroup>"; $app = "<appName>"
New-AzWebAppSlot -ResourceGroupName $rg -Name $app -Slot "staging" -AppServicePlan "<planName>"
# Deploy to 'staging' via your CI/CD, then:
Switch-AzWebAppSlot -ResourceGroupName $rg -Name $app -SourceSlotName "staging" -DestinationSlotName "production"
FAQs
- Q: Will environment variables swap?
A: Only if not marked as “slot setting.” Mark secrets as slot-sticky to keep them in place. - Q: How to roll back fast?
A: Swap back or redeploy the last good build; keep short release notes with build IDs.
Key Points
- Run smoke tests and health checks on staging before swap.
- Warm up the slot to avoid cold-start latency after swap.
Containers & Docker Support
For full control, deploy your own container image. Use ACR with managed identity pulls. Multi-container apps are supported via Docker Compose on Linux. Keep images lean and externalize configuration via App Settings.
Troubleshooting: Container Start
# Check container logs
az webapp log tail -g <rg> -n <app>
# Verify startup command
az webapp config container show -g <rg> -n <app>
FAQs
- Q: Do I need a custom image for every app?
A: Not always; built-in runtimes are simpler. Use custom images when you need custom dependencies. - Q: Can I mount persistent storage?
A: Yes—Azure Storage can be mounted for certain scenarios; design for statelessness where possible.
Key Points
- Use readiness/liveness endpoints and set WEBSITES_PORT if needed.
- Enable Continuous Deployment from ACR for new tags.
Global Availability & Pricing Tiers
Deploy to multiple regions for resilience and latency reduction. Plans range from Free/Shared for experiments to Premium v3 and Isolated v2 for enterprise. Use autoscale + reserved instances to balance cost and performance.
FAQs
- Q: When do I need Isolated/ASE?
A: When you require dedicated compute, advanced network isolation, or strict compliance boundaries. - Q: How to model costs?
A: Right-size instance count, use autoscale, and minimize cold standby where feasible.
Key Points
- Place stateful data in managed services (SQL, Cosmos DB) with geo-replication.
- Front apps with CDN or Front Door for global routing.
Custom Domains, SSL/TLS, and Security
Bind custom domains and use free App Service Managed Certificates or your own certs (Key Vault recommended). Enforce HTTPS, set minimum TLS, enable HSTS, and prefer managed identities over connection strings wherever possible.
PowerShell: Key Vault-Backed Cert Binding
# Assign a certificate from Key Vault to App Service (simplified flow)
$rg="<rg>"; $app="<app>"; $kv="<keyVaultName>"; $certName="<certName>"
$kvResId = (Get-AzKeyVault -VaultName $kv).ResourceId
New-AzWebAppSSLBinding -ResourceGroupName $rg -Name $app -CertificateName $certName -KeyVaultId $kvResId -SslState SniEnabled -DomainName "<hostName>"
FAQs
- Q: Free cert vs Key Vault cert?
A: Free managed certs are easy but limited; use Key Vault for advanced scenarios and automation. - Q: How to rotate secrets?
A: Prefer managed identities with Key Vault references; rotate automatically on renewal.
Key Points
- Set HTTPS Only, enforce TLS 1.2+, enable HSTS at your edge.
- Use Key Vault references and system-assigned identity.
Monitoring with Application Insights & Diagnostics
App Insights provides distributed traces, live metrics, failures, and dependency maps. App Service diagnostics (and Kudu) provide deep platform logs, process explorers, and profiling. Stream logs during incident response.
CLI: Enable Log Streaming & Health Checks
# Enable logging and stream
az webapp log config -g <rg> -n <app> --application-logging filesystem --level information
az webapp log tail -g <rg> -n <app>
# Configure health check path
az webapp config set -g <rg> -n <app> --generic-configurations "{'healthCheckPath':'/health'}"
Kusto Query (App Insights)
requests
| where timestamp > ago(1h)
| summarize count() by resultCode
| order by count_ desc
FAQs
- Q: Logs missing after swap?
A: Ensure slot-specific instrumentation keys/connection strings are slot-sticky. - Q: How to reduce sampling bias?
A: Tune sampling rates and use adaptive sampling for high-traffic apps.
Key Points
- Use live metrics during incidents; export to Log Analytics for long-term analysis.
- Enable health probes and define meaningful 2xx/5xx thresholds.
Dev/Test/Prod Environments & Easy Rollback
Model dev→test→stage→prod with slots or separate apps per environment. Tag resources, enforce approvals, and keep release notes per build. Roll back by slot swap or redeploying the previous artifact quickly.
PowerShell: Instant Rollback
# Redeploy the last successful artifact from staging (example flow)
# Requires that your CI preserved artifact paths or used Run-From-Package
$rg="<rg>"; $app="<app>"
$packageUri="<sasOrArtifactUrl>"
Publish-AzWebApp -ResourceGroupName $rg -Name $app -ArchivePath $packageUri
FAQs
- Q: Should DB migrations run before or after swap?
A: Prefer backward-compatible migrations before swap; use feature flags to decouple risk. - Q: Can each slot have different secrets?
A: Yes—mark app settings as “slot setting.”
Key Points
- Automate database migrations; be migration-aware in rollbacks.
- Keep deployment artifacts immutable and traceable.
Hybrid Connectivity: VNet Integration & Private Endpoints
Securely reach on-premises or private PaaS resources (SQL, Storage, Cosmos DB) via regional VNet integration and Private Endpoints. Use DNS correctly; many “cannot connect to DB” incidents are DNS or firewall misconfigurations.
CLI: Check VNet Integration
az webapp vnet-integration list --name <app> --resource-group <rg>
# Verify outbound route and DNS resolution via Kudu Console (tcpping, nameresolver)
FAQs
- Q: Can inbound traffic be private only?
A: Use Private Endpoints with Private DNS zones and restrict public access at the edge. - Q: Common VNet pitfalls?
A: Missing route tables, DNS split-horizon issues, or NSG blocking required ports.
Key Points
- Document DNS zones and link them correctly to VNets.
- Audit connection strings; prefer managed identities + Key Vault.
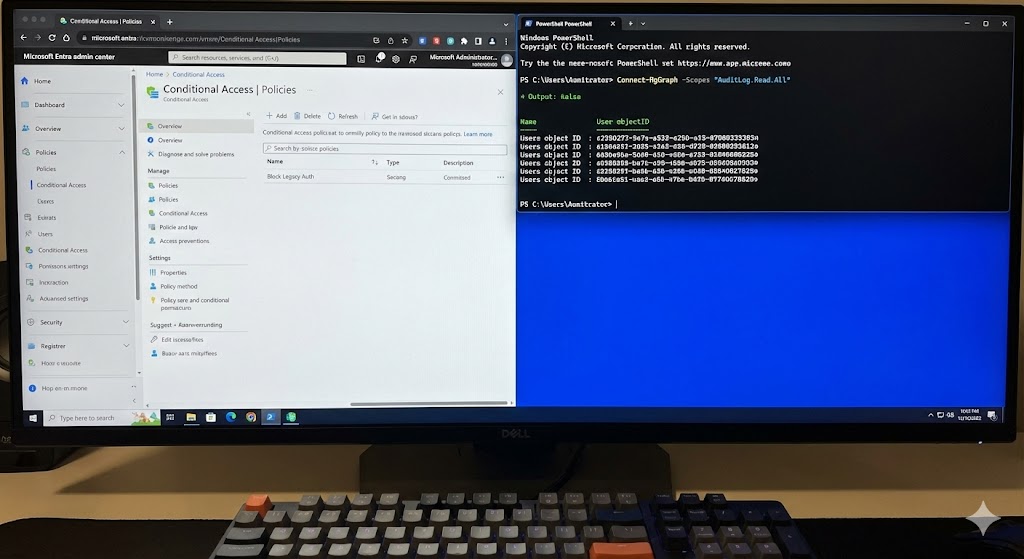
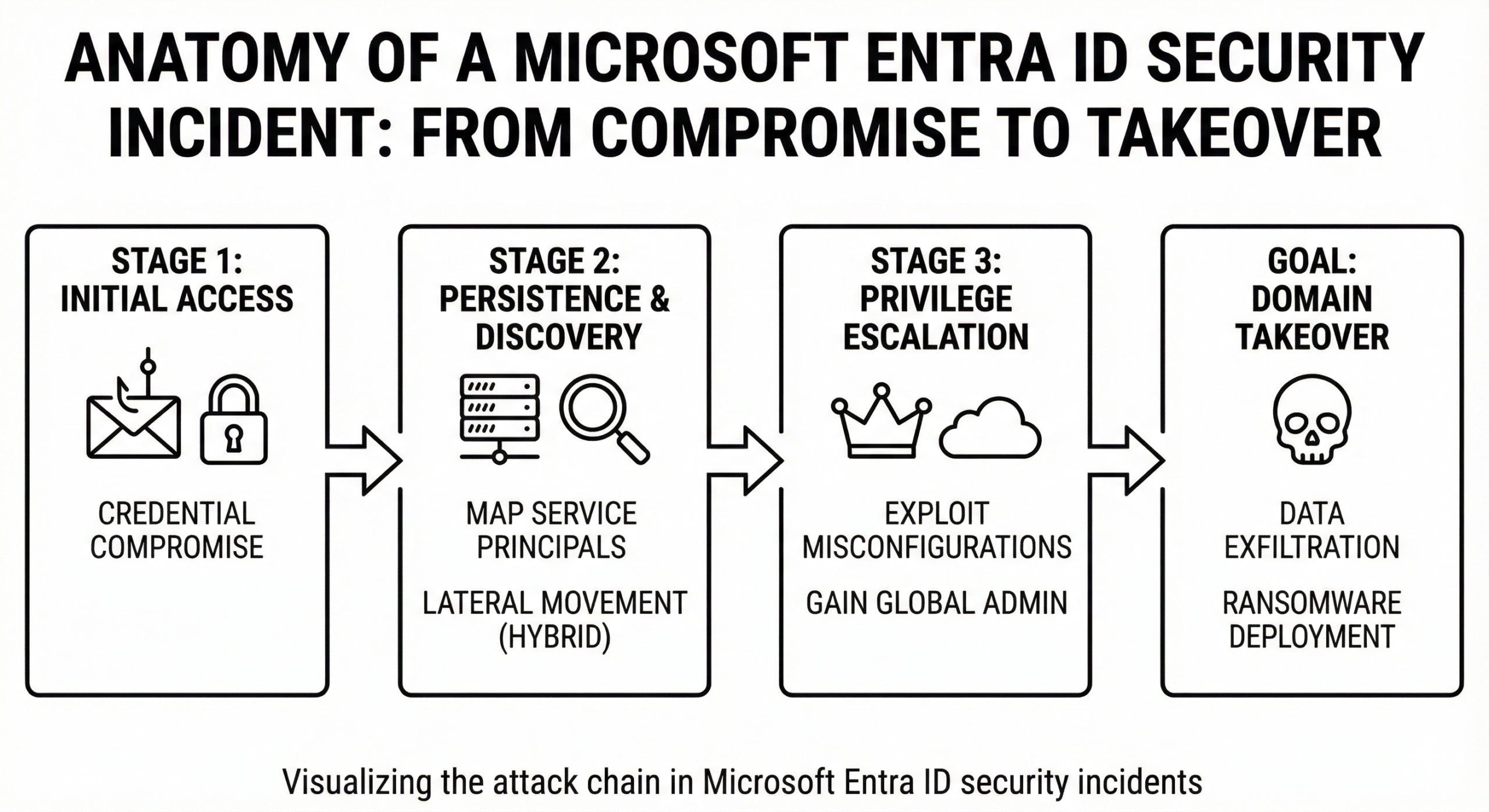
Security, Compliance, and Entra ID (Azure AD) Integration
App Service meets major compliance programs (ISO, SOC, GDPR, HIPAA). Integrate apps with Entra ID for single sign-on, OAuth2/OIDC, and role-based access. Use App Roles/Groups claims and enforce conditional access at the tenant level.
Graph API: Quick Sign-in Log Check (Troubleshooting)
# Requires Microsoft.Graph PowerShell SDK (Connect-MgGraph -Scopes AuditLog.Read.All)
# Find failed sign-ins for the app (by AppId)
$appId="<your-appId-guid>"
Get-MgAuditLogSignIn -Filter "appId eq '$appId' and status/errorCode ne 0" -All `
| Select-Object createdDateTime,userDisplayName,ipAddress,appDisplayName,status
PowerShell: Validate App Role Assignment
# Ensure a user/group has a required App Role on the Enterprise App
# Scopes: Application.Read.All, AppRoleAssignment.ReadWrite.All (admin consent)
$sp = Get-MgServicePrincipal -Filter "appId eq '$appId'"
Get-MgServicePrincipalAppRoleAssignedTo -ServicePrincipalId $sp.Id `
| Select-Object principalDisplayName,appRoleId,principalType
FAQs
- Q: 401 after login?
A: Check reply URLs, scopes/roles, and audience (App ID URI). Validate tokens and time skew. - Q: Need multi-tenant auth?
A: Set the app to multi-tenant in App Registrations and adjust issuer validation.
Key Points
- Protect privileged routes with groups/roles claims.
- Use Conditional Access for MFA, device compliance, and location policies.
Custom Startup Scripts
Start commands let you initialize dependencies, run migrations, or set environment config during boot. For Linux,
configure a startup command or provide a startup.sh in your repo or image.
#!/bin/bash
# startup.sh example
python manage.py migrate --noinput || echo "Migrations skipped"
gunicorn app.wsgi --bind=0.0.0.0:${PORT:-8080} --workers=4
FAQs
- Q: Where to set startup command?
A: In App Settings (“Startup Command”) or via container CMD/ENTRYPOINT. - Q: Debugging failed boot?
A: Use Kudu, log stream, and review Docker stdout/stderr.
Key Points
- Keep idempotent scripts; avoid long blocking tasks during boot.
- Prefer database migrations in pipelines with rollback safeguards.
Automated Backups & Restore
Schedule backups (content + DB) to Storage Accounts. For database consistency, orchestrate application quiesce or use native DB backup features (Azure SQL automated backups).
# CLI: Trigger a one-time backup (example for Linux web app)
az webapp config backup create --resource-group <rg> --webapp-name <app> --storage-account-url <sasUrl> --db-name <dbName> --db-connection-string "<connStr>" --db-type SQLAzure
FAQs
- Q: Are free plans backed up?
A: Backups need at least Standard tier. Use repo re-deploy for code; store content in source control. - Q: Point-in-time restore?
A: Use Azure SQL PITR and redeploy code artifacts.
Key Points
- Test restores regularly; verify connection strings and keys.
- Document RPO/RTO and align schedules.
API & Mobile Backend Hosting
Host REST APIs with swagger/OpenAPI, integrate with APIM for security and throttling, and use Functions for event triggers. Mobile apps benefit from push notifications and auth via Entra ID or social providers.
# Quick OpenAPI publishing tip (Node/Express)
# Serve swagger.json at /swagger/v1/swagger.json and protect /swagger with auth in production
FAQs
- Q: Where to place API keys?
A: Use Key Vault + managed identity; avoid storing keys in appsettings.json. - Q: Rate limiting?
A: Put APIM in front; add per-subscription quotas and JWT validation policies.
Key Points
- Prefer OIDC with scopes/roles over static API keys.
- Enable CORS minimally; avoid wildcard origins in production.
Deployment Methods
Choose from GitHub Actions, Azure DevOps, Local Git, ZIP Deploy, Run-From-Package, or ARM/Bicep/Terraform. For containers, push to ACR and configure continuous deployment on tag changes.
# ZIP Deploy (Run-From-Package recommended)
az webapp deploy --resource-group <rg> --name <app> --src-path "./site.zip" --type zip
# or
az webapp deploy --resource-group <rg> --name <app> --src-path "./app.jar" --type jar
FAQs
- Q: Why run-from-package?
A: Immutable deployments, faster startup, and fewer file lock issues. - Q: Can I use ARM/Bicep for everything?
A: Yes—infra as code for plans, apps, slots, settings, and monitoring.
Key Points
- Separate infra (Bicep/Terraform) from app artifacts.
- Keep slot settings for secrets stable across swaps.
App Settings & Configuration Management
Use App Settings for environment variables; mark as slot-sticky. Prefer Key Vault references with managed identities and store connection strings as secrets (not in code). Audit changes with Activity Logs.
# CLI: Set slot-sticky setting
az webapp config appsettings set -g <rg> -n <app> --settings "Api__BaseUrl=https://api.contoso.com"
az webapp config appsettings set -g <rg> -n <app> --slot-settings "Api__Key=@Microsoft.KeyVault(SecretUri=<secretUri>)"
FAQs
- Q: Are Key Vault references dynamic?
A: The platform refreshes them; restart if you need immediate pickup. - Q: How to audit who changed an app setting?
A: Use Activity Logs and Azure Policy for guardrails.
Key Points
- Never commit secrets to Git; use managed identities.
- Use feature flags (e.g., App Configuration) to de-risk releases.
Custom Logging, Kudu, and Real-Time Troubleshooting
Kudu (Advanced Tools) exposes a web console, process explorer, environment variables, and site file system. It’s invaluable during cold starts, deployment issues, and permission errors.
# Kudu (SSH/Console) quick actions:
# - tcpping <host> <port> # test TCP connectivity
# - curl -I https://<url> # check headers/HTTPS
# - SET / printenv # view env vars
FAQs
- Q: High CPU from w3wp/node?
A: Use Process Explorer, capture memory dump, and correlate with App Insights traces. - Q: 500.30 (ASP.NET Core)?
A: Check hosting bundle, stdout logs, and application event logs via Kudu.
Key Points
- Enable detailed error logs only during incidents; disable afterward.
- Automate log collection in CI for post-mortems.
Serverless Integration with Azure Functions
Offload background tasks to Functions (queues, timers, Service Bus). Share auth (Entra ID) and secrets (Key Vault). Keep APIs in App Service and async jobs in Functions for cost-effective scale.
# Example: API writes to queue; Function consumes and processes
# Use durable functions for orchestrations and retries
FAQs
- Q: Cross-app auth?
A: Use Entra ID with audience restrictions and managed identities for inter-service calls. - Q: Long-running jobs?
A: Use Durable Functions with checkpoints.
Key Points
- Keep API responsive; move heavy work off the request thread.
- Use retry policies and idempotency keys.
Developer Productivity & Rapid Deployment
App Service accelerates release cadence with built-in CI/CD hooks, deployment slots, and diagnostics. It pairs well with trunk-based development and feature flags for incremental delivery with fewer rollbacks.
- Automated builds with unit/integration tests.
- Policy-as-code to enforce HTTPS/TLS and diagnostic settings.
- Observability budgets: define SLOs and error budgets per service.
Bonus SEO Tips for Azure App Service Content
To rank on Google, Bing, and Edge News for Azure App Service, include keywords like Azure CI/CD, GitHub Actions, Azure DevOps integration, App Service auto-scaling, Azure PaaS, web app deployment, Application Insights, and Azure containers. Add internal links to cloudknowledge.in posts on related topics (security, networking, cost optimization).
Quick Troubleshooting Playbook (Copy-Paste)
1) App Down or Slow
az webapp show -g <rg> -n <app> --query "{state: state, httpsOnly: httpsOnly}"
az webapp log tail -g <rg> -n <app>
# App Insights quick failures:
# failures | where timestamp > ago(30m) | summarize count() by type, problemId
2) 500 After Slot Swap
- Validate slot-sticky settings (connection strings, instrumentation keys).
- Compare WEBSITE_RUN_FROM_PACKAGE and framework versions between slots.
3) Auth/SSO Errors
# Graph PowerShell: Find failed sign-ins for your app
Get-MgAuditLogSignIn -Filter "appId eq '<appId>' and status/errorCode ne 0" -All | Select createdDateTime,ipAddress,status
# Validate JWT audience/issuer; check reply URLs and app roles.
4) DB Connectivity Issues (Private Endpoint)
- From Kudu:
nameresolver <fqdn>andtcpping <fqdn> 1433(SQL) or 443 for others. - Verify Private DNS zone link to the VNet and firewall rules.
5) Container Won’t Start
az webapp log tail -g <rg> -n <app>
az webapp config container show -g <rg> -n <app>
# Ensure WEBSITES_PORT equals exposed container port; check CMD/ENTRYPOINT.
Final Thoughts
Azure App Service is a pragmatic sweet spot for most web and API workloads: managed scaling, strong CI/CD integration, and enterprise security without the ops burden of IaaS. Start simple with a Standard plan, add staging slots and health checks, wire up GitHub Actions with OIDC, and evolve toward Premium/Isolated with private networking as you grow.







100
Thank you for your sharing. I am worried that I lack creative ideas. It is your article that makes me full of hope. Thank you. But, I have a question, can you help me? https://www.binance.com/register?ref=IXBIAFVY