The Ultimate Deep Dive: Architecting Microsoft Intune for Zero Trust Security
~25 min read
1. Introduction: Intune is Not Just MDM Anymore
For years, IT professionals viewed Microsoft Intune purely as a Mobile Device Management (MDM) tool—a utility for pushing Wi-Fi profiles, wiping lost iPads, and occasionally deploying an MSI file. But for a modern Cloud Security Engineer, that definition is dangerously outdated.
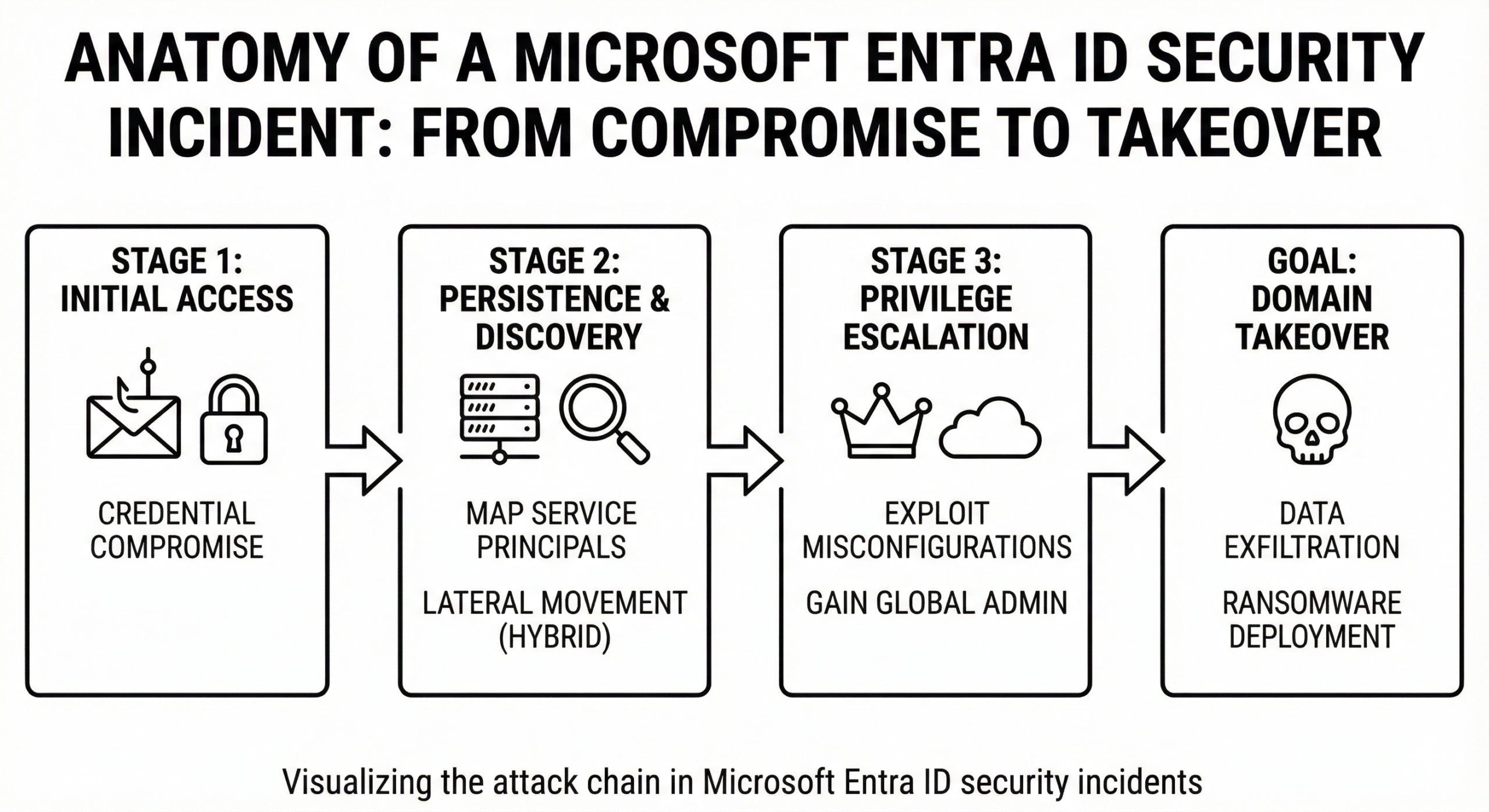
Today, Microsoft Intune (part of the Microsoft Intune family of products) is the enforcement arm of the Zero Trust architecture. It is the bridge between device health, identity access, and data protection. In a world where the perimeter is no longer the corporate firewall but the identity and the endpoint, Intune is your primary defense mechanism against token theft, lateral movement, and data exfiltration.
In this comprehensive, 5000-word deep dive, we are bypassing the basic UI click-throughs. We are looking at Intune through the lens of offensive security and defensive architecture. We will explore how Configuration Service Providers (CSPs) actually process payloads, how to architect foolproof Conditional Access policies, the nuances of Attack Surface Reduction (ASR), and how to deploy custom Proactive Remediations to hunt for vulnerabilities on the endpoint.
2. The Anatomy of Intune Security & Policy Precedence
Before deploying a single policy, a Cloud Security Engineer must understand how Intune delivers payloads to Windows endpoints. Unlike traditional Active Directory Group Policy Objects (GPOs) that refresh on a predictable 90-minute cycle via SMB pull, Intune utilizes the Windows Notification Service (WNS) and OMA-DM (Open Mobile Alliance Device Management) protocols.
GPO vs. CSP: The Tattooing Dilemma
Traditional GPOs often "tattoo" the registry. If a device falls out of scope of a GPO, the registry key often remains modified until explicitly reversed. Intune policies rely on Configuration Service Providers (CSPs). A CSP is an interface in the client operating system that reads the OMA-URI payload and applies it to the device.
When an Intune profile is removed, the CSP attempts to revert the setting to its default state. However, this is not a universal guarantee. Security engineers must be aware that certain legacy settings (often deployed via ingested ADMX templates) may still tattoo the device, requiring explicit rollback policies.
Conflict Resolution: Who Wins?
When you have thousands of endpoints and dozens of administrators, policy conflicts are inevitable. If Endpoint Admin A deploys a Settings Catalog policy disabling the Windows Firewall, and Security Admin B deploys an Endpoint Security Baseline enforcing it, what happens?
- Intune Native Conflict: If two Intune policies conflict, Intune flags the setting as "Conflict" and does not apply either setting. The device remains in its previous state until the conflict is resolved in the console. This "fail-safe" approach prevents race conditions.
- GPO vs. Intune (MDMWinsOverGPO): By default, if a GPO and an Intune policy clash, GPO wins. However, Security Engineers should implement the
ControlPolicyConflict/MDMWinsOverGPOpolicy. This forces the device to prioritize Intune CSPs over domain-joined GPOs, a critical step when migrating to cloud-native management.
(Applications and Services Logs > Microsoft > Windows > DeviceManagement-Enterprise-Diagnostics-Provider). Detail specific Event IDs (e.g., Event ID 814 for string policy processing) that security engineers should ingest into their SIEM (like Microsoft Sentinel).
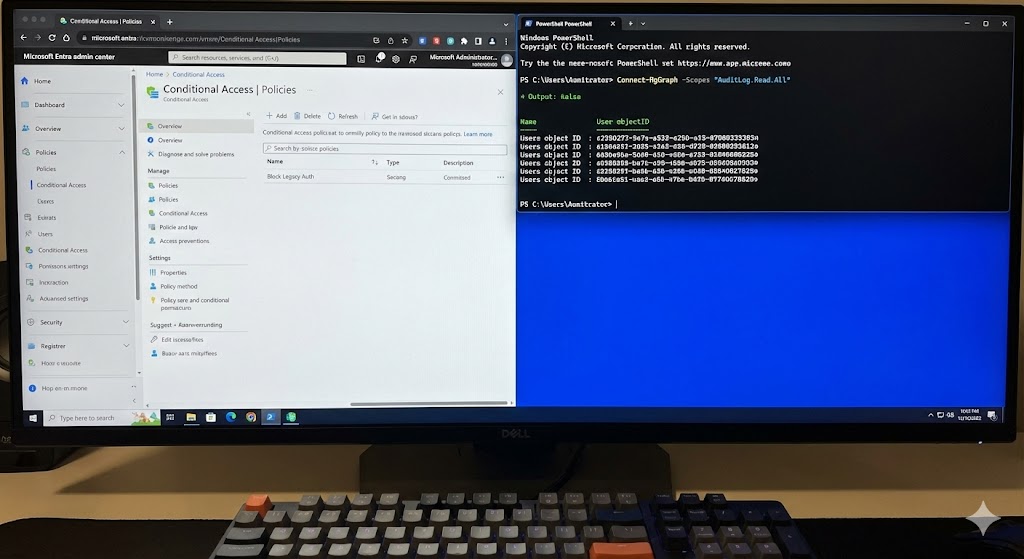
3. The Crown Jewel: Entra ID Conditional Access Integration
Intune's true power is unlocked when integrated with Microsoft Entra ID (formerly Azure AD) Conditional Access. This is the literal definition of Zero Trust: Never trust, always verify.
A device might have valid user credentials and a passing MFA token, but if Intune reports that the device's real-time threat defense (like Microsoft Defender for Endpoint) has detected a malicious payload, Conditional Access can instantly sever the token, blocking access to corporate data.
Architecting Compliance Policies
A Compliance Policy is a binary checklist. The device is either Compliant or Non-Compliant. As a security engineer, your baseline compliance policy should enforce:
- OS Version Minimums: Blocking unpatched, vulnerable builds of Windows 11.
- BitLocker Encryption: Ensuring the OS drive is encrypted with at least XTS-AES 256-bit encryption.
- Firewall Status: Ensuring the host firewall is active.
- Machine Risk Score: (Requires Defender for Endpoint). Setting the acceptable risk score to "Clear" or "Low". If a user downloads malware, the risk score jumps to "High," rendering the device non-compliant instantly.
"Conditional Access without Intune Compliance Policies is like a bouncer checking IDs but ignoring the fact that the person walking in is carrying a weapon. Identity security is only half the battle; endpoint health is the other."
The Grace Period Trap
A common misconfiguration is offering a generous "Grace Period" for non-compliance. If a user disables BitLocker, and your policy allows a 3-day grace period, an attacker has 72 hours to extract cached credentials and access SharePoint data before Entra ID revokes the token. Security recommendation: Set the grace period for critical security controls to "0 days" to enforce immediate token revocation.
4. Hardening Windows: ASR Rules & Security Baselines
Deploying standard settings is one thing; hardening the OS against fileless malware, macro abuse, and credential dumping is another. This is where Attack Surface Reduction (ASR) rules come into play via Intune's Endpoint Security blade.
Implementing ASR Rules
ASR rules are heavily reliant on Microsoft Defender Antivirus. They restrict behaviors commonly used by attackers. Crucial rules to deploy via Intune include:
- Block credential stealing from the Windows local security authority subsystem (lsass.exe): Prevents tools like Mimikatz from dumping credentials from memory.
- Block executable files from running unless they meet a prevalence, age, or trusted list criterion: Stops zero-day executables that lack a reputation score.
- Block Office applications from creating child processes: Neutralizes weaponized Word or Excel documents attempting to spawn PowerShell or CMD.
The "Audit First" Methodology
Pushing ASR rules to "Block" immediately will almost certainly break legacy business applications, resulting in a flood of helpdesk tickets. Security Engineers must utilize Intune to deploy these rules in Audit Mode first. You then query the Advanced Hunting logs in Microsoft Defender XDR to see what would have been blocked. Once exclusions are configured, you flip the switch from Audit to Block.
5. Securing BYOD: Mobile Application Management (MAM)
One of the hardest challenges in Cloud Security is BYOD (Bring Your Own Device). Users refuse to enroll their personal iPhones or Androids into corporate MDM because they fear IT will monitor their personal data or wipe their family photos.
The solution is MAM without Enrollment (MAM-WE), utilizing Intune App Protection Policies (APP).
How App Protection Policies Work
Instead of managing the device, Intune manages the application identity. When a user logs into Outlook on their personal phone, Intune creates a secure, encrypted container exclusively for corporate data within that app.
As a security engineer, you configure the APP to enforce the following:
- Data Relocation Prevention: Block users from copying text from corporate Outlook and pasting it into personal WhatsApp or Apple Notes.
- Save-As Restrictions: Block saving corporate OneDrive files to local device storage.
- App-Level PIN/Biometrics: Require FaceID or a PIN just to open the corporate apps, independent of the device's lock screen.
- Selective Wipe: If the employee leaves the company, Intune can issue a selective wipe that destroys the corporate container inside Outlook/Teams without touching the user's personal apps or data.
6. Advanced Threat Hunting: Proactive Remediations & Custom Scripts
The Settings Catalog is vast, but it doesn't cover everything. Advanced persistent threats (APTs) often manipulate obscure registry keys or establish persistence via scheduled tasks that standard UI toggles can't reach. This is where Proactive Remediations become a Security Engineer's best friend.
The Detection & Remediation Paradigm
Proactive Remediations utilize PowerShell scripts deployed via the Intune Management Extension (IME). They run on a defined schedule (e.g., every hour) and consist of two parts:
- Detection Script: Returns an Exit Code 0 if the device is secure. Returns an Exit Code 1 if a vulnerability is detected.
- Remediation Script: Only runs if the Detection Script returns Exit Code 1. It executes code to fix the vulnerability and secure the system.
Example: Hunting for Unauthorized Local Admins
Attackers often escalate privileges and hide a backdoor account in the local Administrators group. Here is a conceptual deployment:
# DETECTION SCRIPT (PowerShell)
$AllowedAdmins = @("Administrator", "LAPS_Admin", "GlobalAdminSID")
$CurrentAdmins = Get-LocalGroupMember -Group "Administrators" | Select-Object -ExpandProperty Name
foreach ($Admin in $CurrentAdmins) {
if ($AllowedAdmins -notcontains $Admin) {
Write-Host "Unauthorized Admin Found: $Admin"
exit 1 # Triggers Remediation
}
}
Write-Host "Local Admins are secure."
exit 0
If the script exits with code 1, Intune immediately fires the Remediation script to strip the unauthorized user from the group, neutralizing the attacker's persistence mechanism before they can act on it.
7. Conclusion & Security Roadmap
Treating Microsoft Intune as a simple configuration utility leaves its most potent security capabilities dormant. For Cloud Security Engineers, Intune is the engine that drives Zero Trust. By mastering policy precedence, tying compliance to Entra ID Conditional Access, hardening the OS with ASR rules, implementing strict App Protection Policies, and utilizing PowerShell for continuous threat remediation, you transform the endpoint from a liability into a fortified perimeter.
Your next steps: Do not implement these changes blindly in production. Create a dedicated ring-based deployment strategy. Start with an IT pilot group, monitor the Intune troubleshooting logs and Defender Advanced Hunting queries, and slowly expand your hardened baselines across the enterprise.






Leave a Reply